This article explains what phishing is and how to prevent falling victim to it. You may fall victim to a Phishing scam if you open an email that appears to be from a legitimate source.
Sending phony emails that look to come from a trusted source is known as “phishing.” In most cases, this is accomplished by email. The intention is to steal or infect the victim’s computer with malicious code, such as credit card or login information.
A widespread form of cyber attack, phishing, is one that everyone should get familiar with to defend themselves.
5 Ways to Protect Against Phishing Attacks
What is Phishing?
Fake emails or other communications are the first steps in the phishing process. The message appears to have been sent by a reputable source.
This method involves duping people into handing over their personal information to scam websites.
Some malware may also be installed on the victim’s computer.

This is the most usual situation:
Once you open your email, you get a bank alert; your bank’s website appears when you click on the link in the email you received.
Is this site genuinely designed to steal your personal information? That’s what I’m getting at. The notification will prompt you to confirm your login and password.
These threats can be highly complex and appear in all communication forms, including phone calls. Phishing can trick people if they aren’t paying attention.
Phishing attacks provide what kinds of risks?
Getting a victim’s credit card number or other personal information is often enough for an attacker to be happy.
Phishing emails can also gather employee information in more sophisticated attacks on companies.
Phishing is a common starting point for advanced persistent threats (APTs) and ransomware attacks.
Related:
Phishing can be classified into several categories.
There are a variety of phishing scams out there nowadays. As a result, being the victim of fake emails requires special attention.
The following paragraphs provide an overview of some of the most common types of Phishing.
- Spear Phishing: Spear Phishing is something to target a particular individual by sending them a Phishing email or any other means. This type of Phishing is most successful on the internet today, accounting for about 90% of all.
- Email phishing: The most frequently utilized method of sending phishing emails is via email. This person sets up a bogus domain to impersonate a well-known company and then floods it with thousands of automated requests.
- Clone Phishing: Clone Phishing is similar to the user’s email from a genuine authority. The email address was spoofed to appear to come from the original sender. Clone Phishing sends you a similar format email and may ask you to resend the attachments or files you have sent or that email contains a malicious version.
- Whaling: Senior executives are the primary targets of whaling assaults, whaling has the same purpose as any other phishing assault, but it is far more subtle in its execution.
- Deceptive Phishing: Sometimes, messages come out and ask for resubmission of your account credentials or to verify account information.
- Angler phishing: Social networking is a relatively new attack vector that provides thieves many options for duping unsuspecting victims. It’s possible to trick individuals into disclosing personal information or downloading malicious software by sending them unnatural links, creating fake posts and tweets, and using cloned versions of popular social media platforms like Twitter and Facebook.
- Phone Phishing: Sometimes, Phishing comes out by phone. Phishing messages come out and ask to call on given number regarding a problem with their bank account, and then they may ask for login credentials.
Tips to Protect yourself against Phishing Threats
1. Identify Phishing emails
Some tips for suspecting Phishing emails
- Sites seem to be visually similar to existing websites.
- Due to this issue, your name is hidden in the email. Dear customer/client, it appears to be a scam email.
- They are promoting expensive winning gifts by clicking on their link.
2. Use secure websites for your sensitive data
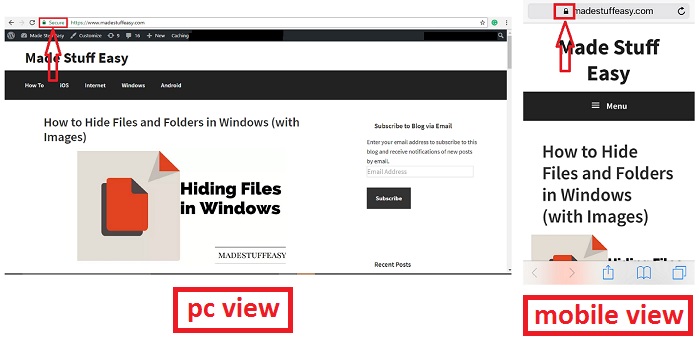
Always use secure websites for your sensitive data information, as they do not share your information publically. You can quickly identify it by having HTTPS show an icon with a closed lock.
See the below screenshot.
3. Check your account periodically
No matter how busy you are in your life, we always recommend our readers check your accounts regularly.
And also, try to keep the password updated and secure the account using 2FA during login. You can also try some of the best password managers to provide a secure password.
And the most important of all, constantly update that phone number which you always have with you.
4. Use Anti-Virus on your PC
Malware protection Antivirus software is always good for preventing external attacks on your computer and sensitive data. Always keep your PC up to date when there is a security concern.

There are many antiviruses. Check Sophos Home Premium Deals.
Sophos Home Premium Discount Offers
5. Ignore links connected to your bank
Never open those links that sometimes appear on your screen and show you as a direct link to your bank account.
Always avoid these types of links to stay safe from Phishing.
You may also like:
We hope you are aware of the dangers posed by phishing and how much of an impact it can have on your life if you aren’t mindful. I hope this tutorial has given you a better understanding of current cyber attacks.
Keep in touch with us for more helpful information on Facebook and Twitter.